Internet Fascism and the Surveillance Stateby Ben O'NeillMises Institute Jul. 15, 2013 |
Popular 
Claim Jewish Student Was 'Stabbed In The Eye' by Pro-Palestine Protester Draws Mockery After Video Released

Mistrial Declared in Case of Arizona Rancher Accused of Killing Migrant Trespasser

Sen. Hawley: Send National Guard to Crush Pro-Palestine Protests Like 'Eisenhower Sent the 101st to Little Rock'

Senate Passes $95B Giveaway to Israel, Ukraine, and Taiwan, Combined With TikTok Ban

AP: 'Israeli Strikes on Gaza City of Rafah Kill 22, Mostly Children, as U.S. Advances Aid Package'
 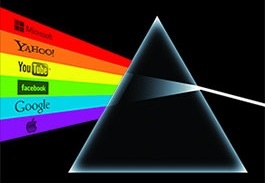 What is the purpose of telecommunication and internet surveillance? What is the purpose of telecommunication and internet surveillance?The NSA presents its surveillance operations as being directed toward security issues, claiming that the programs are needed to counter terrorist attacks. Bald assertions of plots foiled are intended to bolster this claim.[1] However, secret NSA documents reveal that their surveillance is used to gather intelligence to achieve political goals for the US government. Agency documents show extensive surveillance of communications from allied governments, including the targeting of embassies and missions.[2] Reports from an NSA whistleblower also allege that the agency has targeted and intercepted communications from a range of high-level political and judicial officials, anti-war groups, US banking firms and other major companies and non-government organizations.[3] This suggests that the goal of surveillance is the further political empowerment of the NSA and the US government. Ostensibly, the goal of the NSA surveillance is to prevent terrorist acts that would harm or kill people in the United States. But in reality, the primary goal is to enable greater control of that population (and others) by the US government. When questioned about this issue, NSA whistleblower Thomas Drake was unequivocal about the goal of the NSA: "to own the internet and find out what everybody is doing."[4] "To own the internet" -- Public-private partnerships in mass surveillance The internet is, by its very nature, a decentralized arrangement, created by the interaction of many private and government servers operating on telecommunications networks throughout the world. This has always been a major bugbear of advocates for government control, who have denigrated this decentralized arrangement as being "lawless." Since it began to expand as a tool of mass communication for ordinary people, advocates for greater government power have fought a long battle to bring the internet "under control" -- i.e., under their control. The goal of government "ownership of the internet" entails accessing the facilities that route traffic through the network. This is gradually being done through government control of the network infrastructure and the gradual domination of the primary telecommunications and internet companies that provide the facilities for routing traffic through the network. Indeed, one noteworthy aspect of the mass surveillance system of the NSA is that it has allegedly involved extensive cooperation with many "private" firms operating under US law. This has allegedly included major security, telecommunications and internet companies, as well as producers of network software and hardware. Examples of such "public-private partnerships" are set out in leaked documents of the NSA. An unnamed US telecommunications company is reported to provide the NSA with mass surveillance data on the communications of non-US people under its FAIRVIEW program.[5] Several major computing and internet companies have also been explicitly named in top secret internal NSA material as being current providers for the agency under its PRISM program.[6] Several of these companies have issued denials disavowing any participation in, or prior knowledge of the program, but this has been met with some scepticism.[7] (Indeed, given that the NSA did not anticipate public release of its own internal training material, it is unlikely that the agency would have any cause to lie about the companies they work with in this material. This suggests that the material may be accurate.) Many of these companies have supplied the NSA with data from their own customers, or created systems which allow the agency access to the information flowing through telecommunications networks. They have done so without disclosure to their own customers of the surveillance that has occurred, by using the blanket advisement that they "comply with lawful requests for information." By virtue of being subject to the jurisdiction of US statutes, all of these companies have been legally prohibited from discussing any of their dealings with the NSA and they have been well placed for retaliatory action by the many regulatory agencies of the US government if they do not cooperate. In any case, it appears from present reports that many companies have been active partners of the agency, assisting the NSA with illegal surveillance activities by supplying data under programs with no legitimate legal basis. This has been a common historical pattern in the rise of totalitarian States, which have often sought to incorporate large business concerns into their network of power. Indeed, the very notion of "public-private partnerships" in this sector readily brings to mind the worst aspects of fascist economic systems that have historically existed. The actions of US companies that have cooperated in the NSA's mass surveillance operations calls into question the "private" status of these companies. In many ways these companies have acted as an extension of the US government, providing information illegally, in exchange for privileges and intelligence. According to media reports, "Such cooperation is an extremely delicate issue for the companies involved. Many have promised their customers data confidentiality in their terms and conditions. Furthermore, they are obliged to follow the laws of the countries in which they do business. As such, their cooperation deals with the NSA are top secret. Even in internal NSA documents, they are only referred to by the use of code names."[8] We began this discussion by asking the purpose of telecommunication and internet surveillance. The answer lies in the uses to which those surveillance powers are being put, and will inevitably be put, as the capacity of the NSA expands. The true purpose of the NSA is not to keep us safe. Its goal is to own the internet, to own our communications, to own our private thoughts -- to own us. _ Ben O'Neill is a lecturer in statistics at the University of New South Wales (ADFA) in Canberra, Australia. He has formerly practiced as a lawyer and as a political adviser in Canberra. He is a Templeton Fellow at the Independent Institute, where he won first prize in the 2009 Sir John Templeton Fellowship essay contest. Send him mail. Notes [1] Mathes, M. (2013) At least 50 spy programs foiled by terror plots: NSA . The Sydney Morning Herald, 19 June 2013. [2] MacAskill, E. (2013) New NSA leaks show how US is bugging its European allies . The Guardian, 1 June 2013. [3] Burghardt, T. (2013) NSA spying and intelligence collection: a giant blackmail machine and "warrantless wiretapping program." Global Research , 24 June 2013. Reports are from NSA whistleblower Russ Tice, who is a former intelligence analyst at the NSA. [4] Wolverton, J. (2012) Classified drips and leaks. The New American, 6 August 2012. Emphasis added. Capitalization of "Internet" removed. [5] Greenwald, G. (2013) The NSA's mass and indiscriminate spying on Brazilians . The Guardian, 7 July 2013. [6] Gelman, B. and Poitras, L. (2013) US, British intelligence mining data from nine US internet companies in broad secret program . The Washington Post, 7 June 2013. See also NSA slides explain the PRISM data-collecting program . The Washington Post, 6 June 2013. [7] McGarry, C. (2013) Page and Zuckerberg say NSA surveillance program is news to them . TechHive, 7 June 2013. [8] Ibid Poitras, p. 3. |



